Some random interesting tidbits:
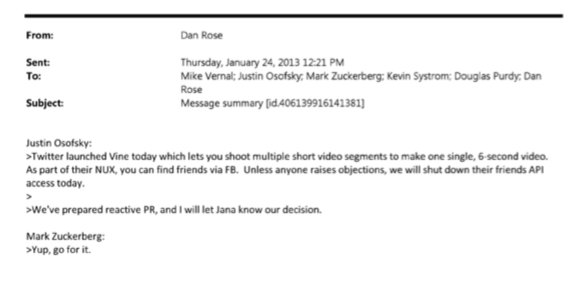
1) Zuck approves shutting down platform API access for Twitter's when Vine is released #competition
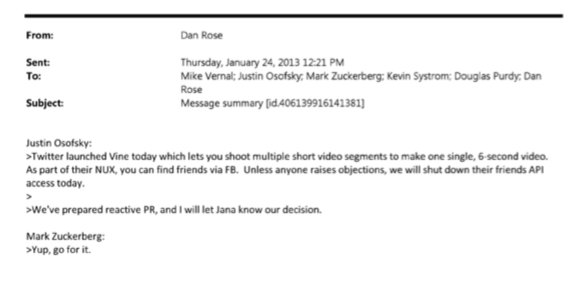
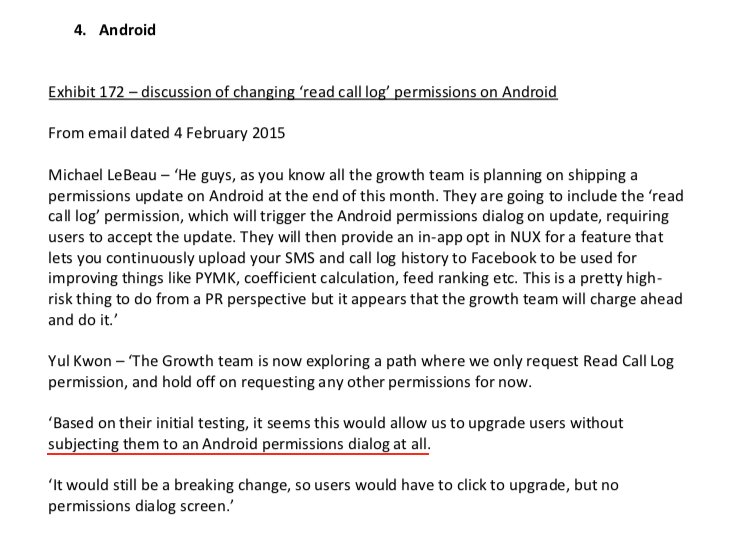
2) Facebook engineered ways to access user's call history w/o alerting users:
Team considered access to call history considered 'high PR risk' but 'growth team will charge ahead'.
@Facebook created upgrade path to access data w/o subjecting users to Android permissions dialogue.
3) The above also confirms
@kashhill and other's suspicion that call history was used to improve PYMK (People You May Know) suggestions and newsfeed rankings.
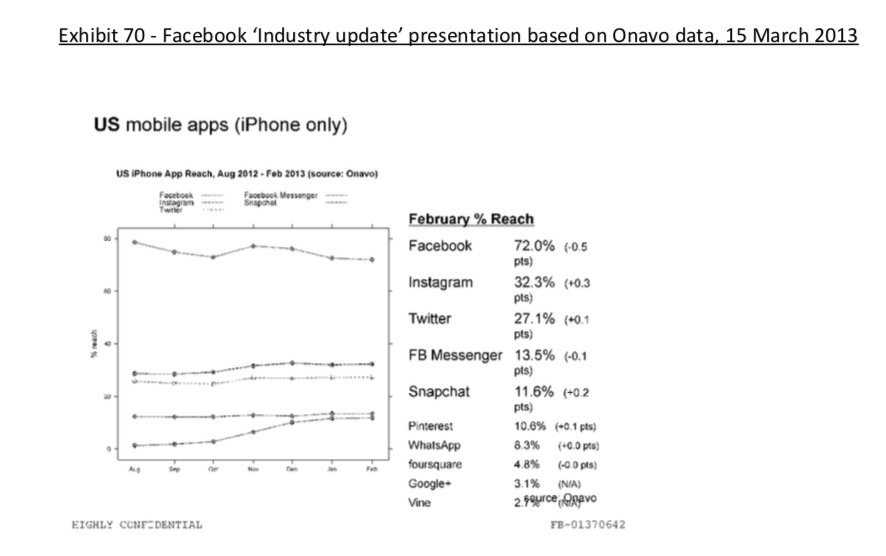
4) Docs also shed more light into
@dseetharaman's story on
@Facebook monitoring users'
@Onavo VPN activity to determine what competitors to mimic or acquire in 2013.
https://t.co/PwiRIL3v9x
5) Interesting contrast regarding "never selling users' data"
6) OK well at least Facebook developers were self aware of their public image (re: bluetooth beacons and call-logs): "Facebook uses new Android update to pry into your private life in ever more terrifying ways - reading your call logs, tracking you in businesses with beacons,etc"
7)
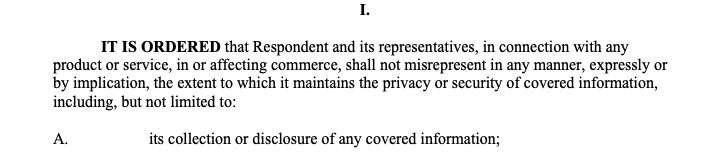
@FTC consent decree required that
@Facebook get 1A) affirmative consent before the collection of covered info 4A) create a privacy program to address privacy risks
However, docs show lead of privacy program was actively working to evade user consent
https://t.co/mcXhDnSg2i
8) Another study in contrasts
@Facebook statements re: Android SMS and Call Log History
1) internal discussion Feb 4 2015
2) public 'clarifying' statement Mar 25 2018
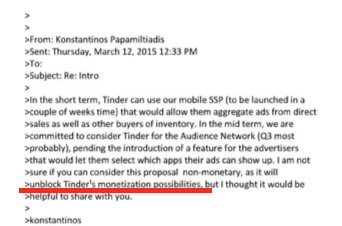
9) Anti-competitive practices can consist of selectively blocking access to the ad network, not just user data:
@Facebook's director of platform offered to 'unblock
@Tinder's monetization possibilities' if
@Tinder permitted use of 'Moments' trademark:
https://t.co/VkJGD4hp5E
10) 2015 exchange re: whitelisted apps with
@Lyft Q: Are there any contracts or other steps besides whitelisting to launch a feature using the APls?
A: You don't need to worry about any contracts for the api. This is a product we are testing and will be rolling out slowly.
11) Facebook rep discusses removal of 'all friends-list in V2 of Facebook API as an indirect way to drive mobile ad adoption
(NEKO is an acronym used to describe mobile app-install ads)
12) Here is the key 'pay for access' evidence that
@DamianCollins hinted at in
@CommonsCMS: Apps need to spend at least $250K/yr on
@Facebook ads (NEKO) in order to maintain access to data. Apps that don't will have data permissions will be revoked. #antitrust #sellingdata
13) In 2012, Vine and Path were the two fastest growing social networking app competitors to Facebook. #wherearetheynow #competition
14) If you read anything, it should be the email from
@Zuck on P49 laying out his vision for platform monetization and growth (echoed by Sandberg).
It most clearly lays out the strategy of the company with regards to platform API and user data:
15) "The fundamental principle that governs Platform usage: reciprocity-an equable value exchange between a 3rd party developer and Facebook" (excluding competitors)
Developers provide:
or direct payment/rev sharing
FB provides: access to platform (userdata/friends)
16) Finally, some might recall this exchange between
@Zuck and friend from a *slightly* older leak (2004) which illustrates that the issue of bartering access to users' information isn't a new one -- it's
@Facebook's primary motivation:
https://t.co/0oh1dGIDvd (ht
@EuanDBriggs)