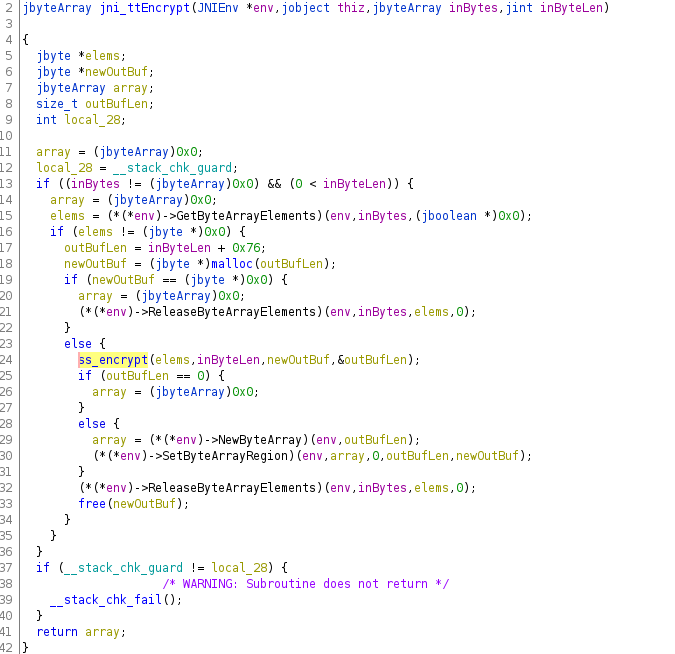
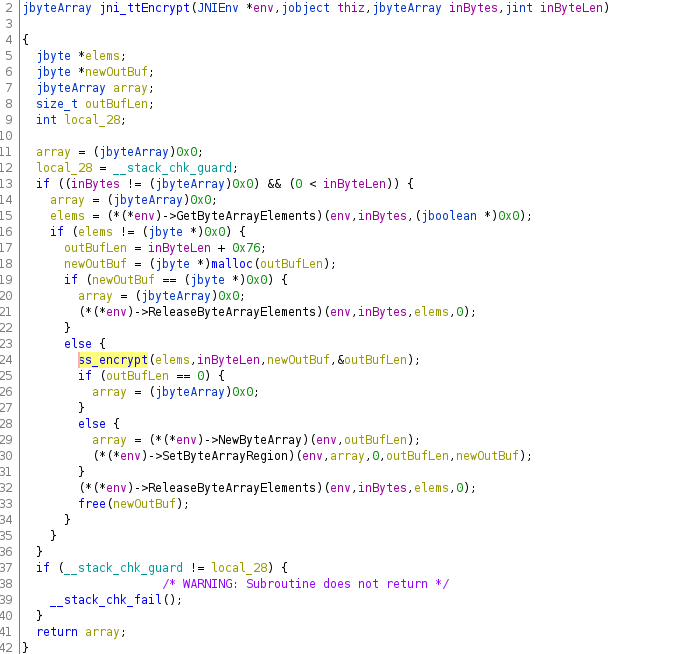
TikTok's (log data) encryption is accomplished by a native library. The Android Java code just serves as proxy function to the native function
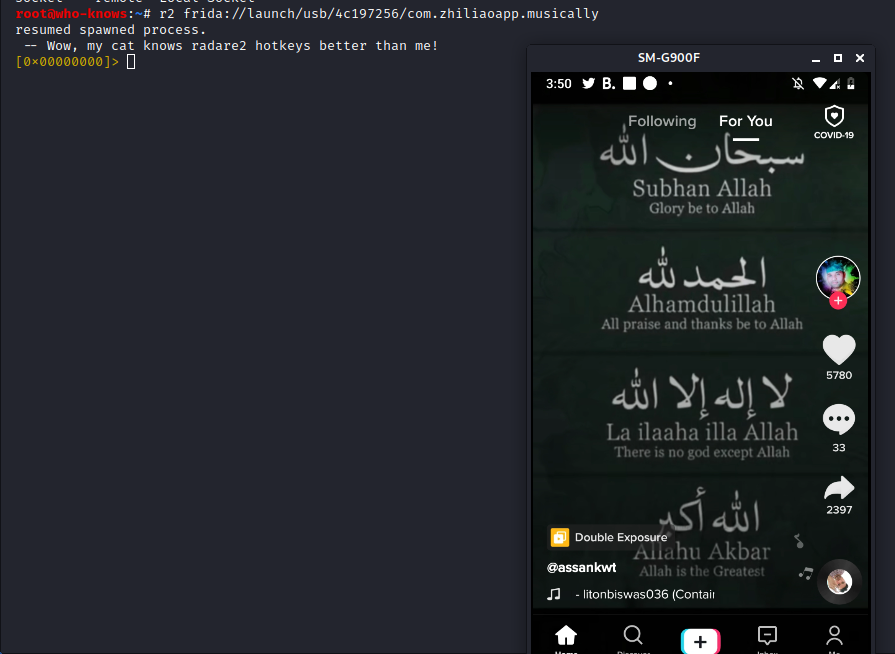
Okay, doing my first baby steps with r2frida (which combines the power of @radareorg and @fridadotre).
Gonna share my progress in this thread (live, so keep calm).
The goal: Runtime inspection of data sent out by TikTok !!before!! it gets encrypted
1/many
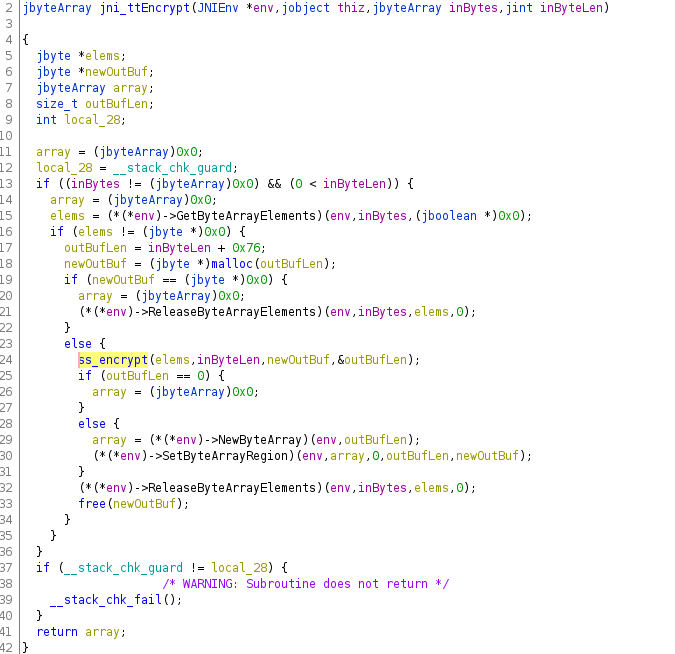
TikTok's (log data) encryption is accomplished by a native library. The Android Java code just serves as proxy function to the native function
https://t.co/T63vo3N4fw
1) Unlike raw C-functions, JNI functions like the one showcased above, receive pointers to complex Java objects .
F.e. a function receiving a String on the Java layer...
In order to retrieve a C-String, to go on working with it in the native code, some translation functionality is required. This functionality is provided by the ...
If you look at the example screenshot again, you see exactly this. Functions provided by the 'env' pointer are used to parse the Java function arguments (f.e. jByteArrays) ...
2) There are two ways to expose JNI methods from a native library:
a) export them with proper naming convention, so that JNI could recognize same on library load
b) use the JNI functionality 'registerNatives'...
The second method of registering methods is wel suited for obfuscated code, as the methods neither have to follow naming convention, nor do they have to be exported.
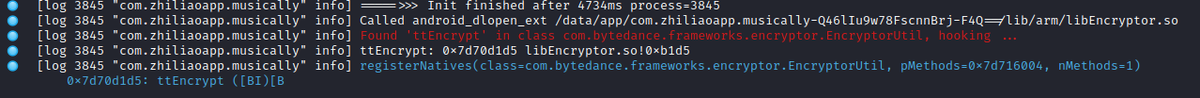
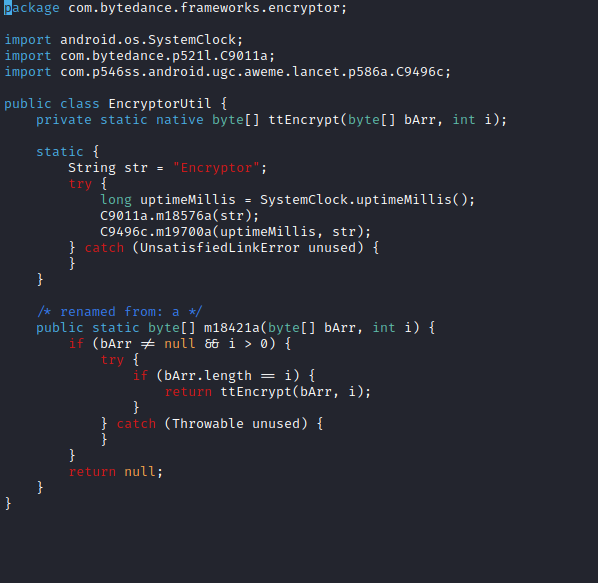
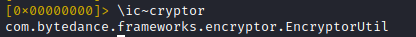
Internally, this data is forwarded to the native JNI method 'ttEncrypt'.
We already saw this signature in a previous screenshot
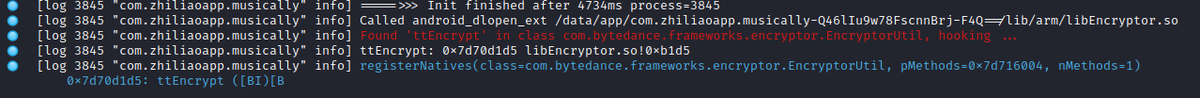
1) the call address of the native function implementation (0x7d70d1d5 in example)
2) The function name (ttEncrypt)
...
'(' start of parameters
'[B' byte[]
'I' int
')' end of parameters
'[B' byte[] (return value)
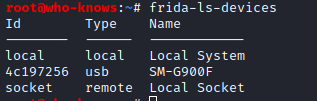
- the app is inspected on a physical device, running Android 9
- the device uses a !!32bit!! ARM application core
Now to get started, I already have the latest @fridadotre server running on my USB connected android device and 'frida-ls-device' shows it being ready-for-action
Instead of 'launch', two other options could be used:
- 'spawn' (like 'launch', but the process would not be resumed automatically after attaching)
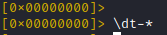
Important: commands targeting the r2frida plugin have to be prefixed with '\'
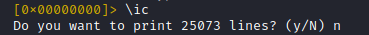
The signature of the static method 'EncryptorUtil.a' should look familiar to us (if you read the first tweets). It represents the Java layer of the encryption method and is called 'a' in this version
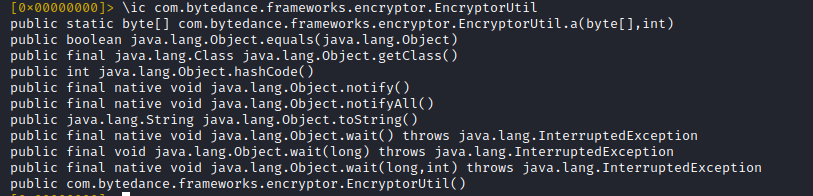
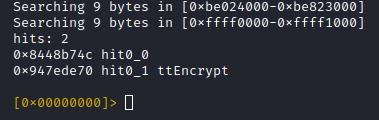
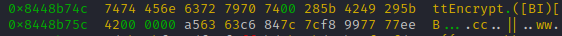
So lets search the whole address space for our native method name 'ttEncrypt'
Note: If you'd use r2's ascii search nothing would happen, you have to use the '\' prefix to search with r2frida
Reason: The memory region was not populated when r2 was started (encryption library was loaded after process launch)
1) Quit r2
2) Open r2 with r2frida, again, but this time **attach** to the already running process
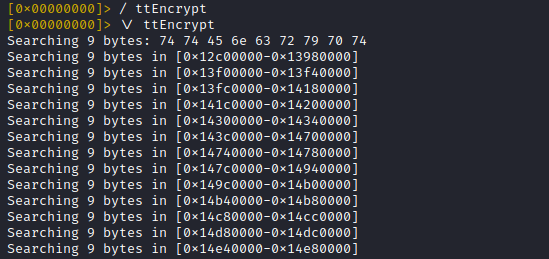
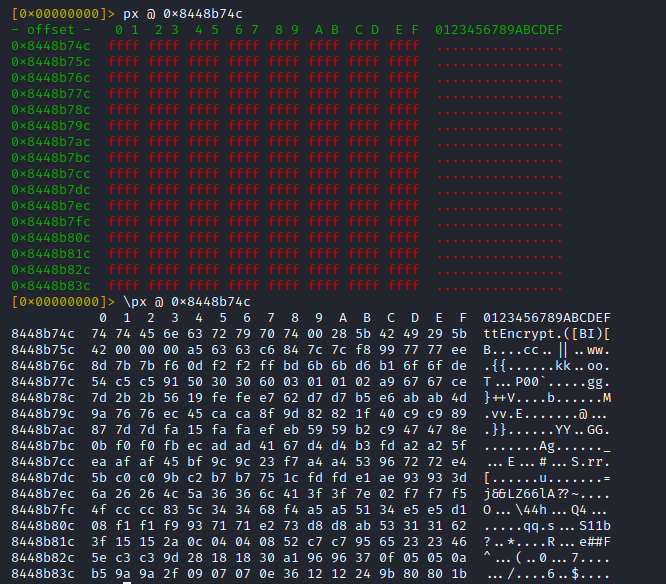
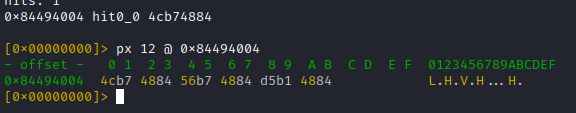
et voila ... the memory offset is mapped and dumpable with 'px' (without backslash prefix)
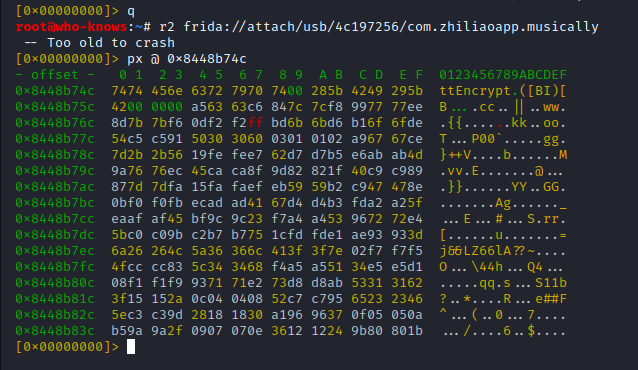
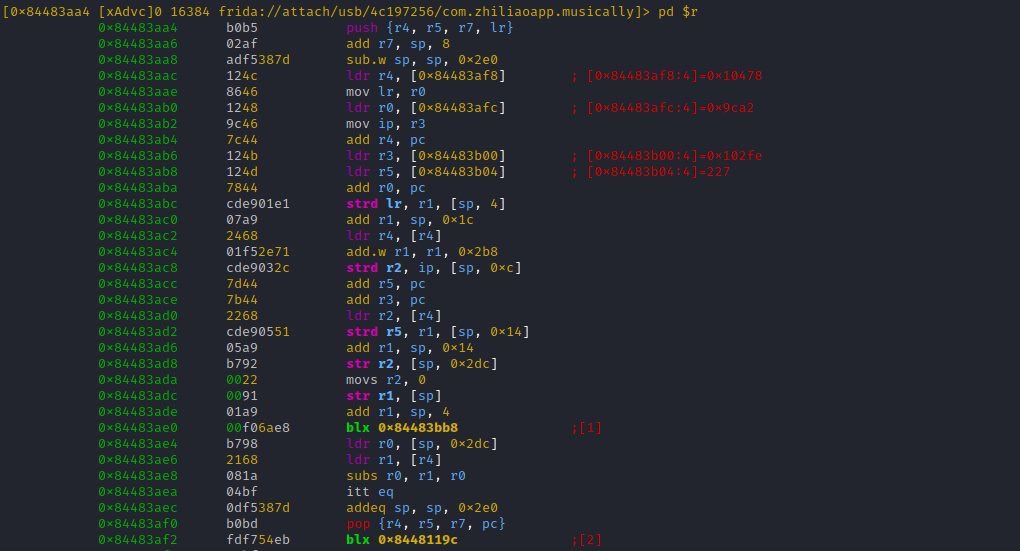
So chances are high, that this data is part of the structure which gets handed in to 'registerNatives'
- method name (C-string)
- method signature (C-string)
- method pointer (native pointer)
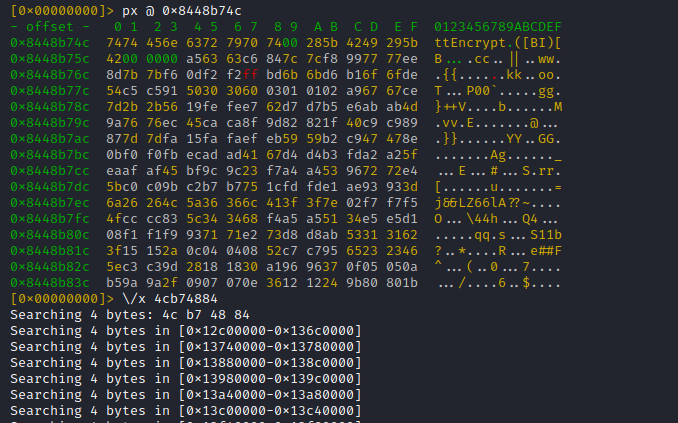
The result is promising: Only one hit, for a search across the whole address space:
- 0x8448b74c (expected, method name pointer)
- 0x8448b756 (ptr to signature string, yay)
- 0x8448b1d5 (likely pointer to JNI method implementation)
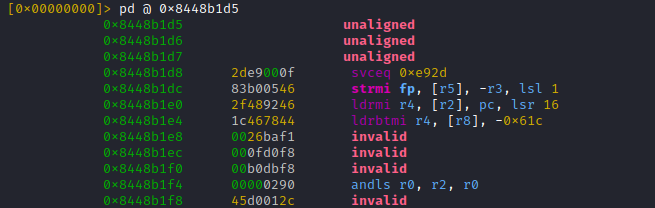
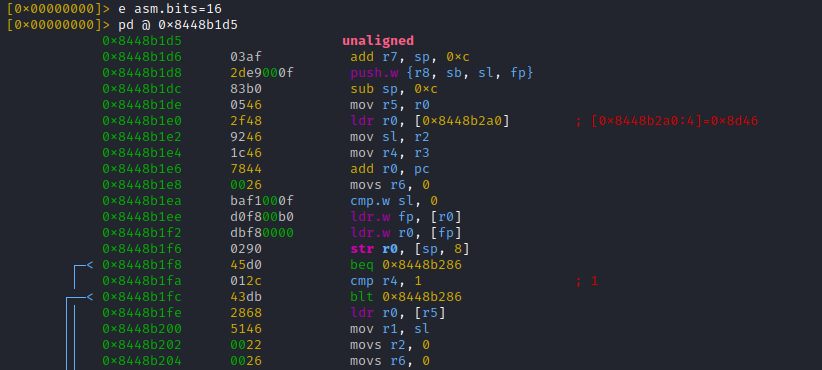
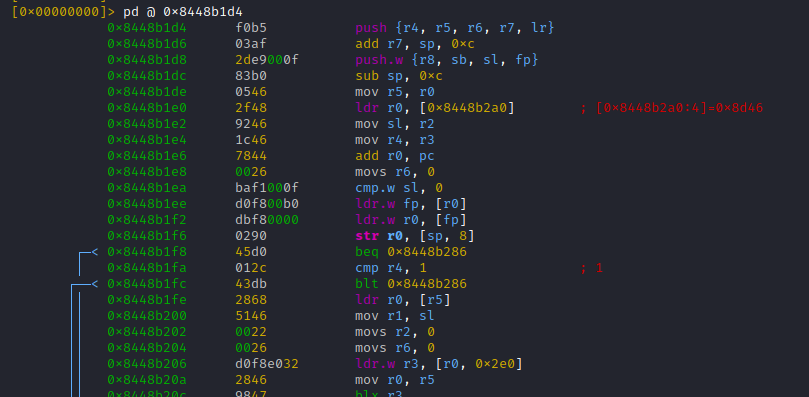
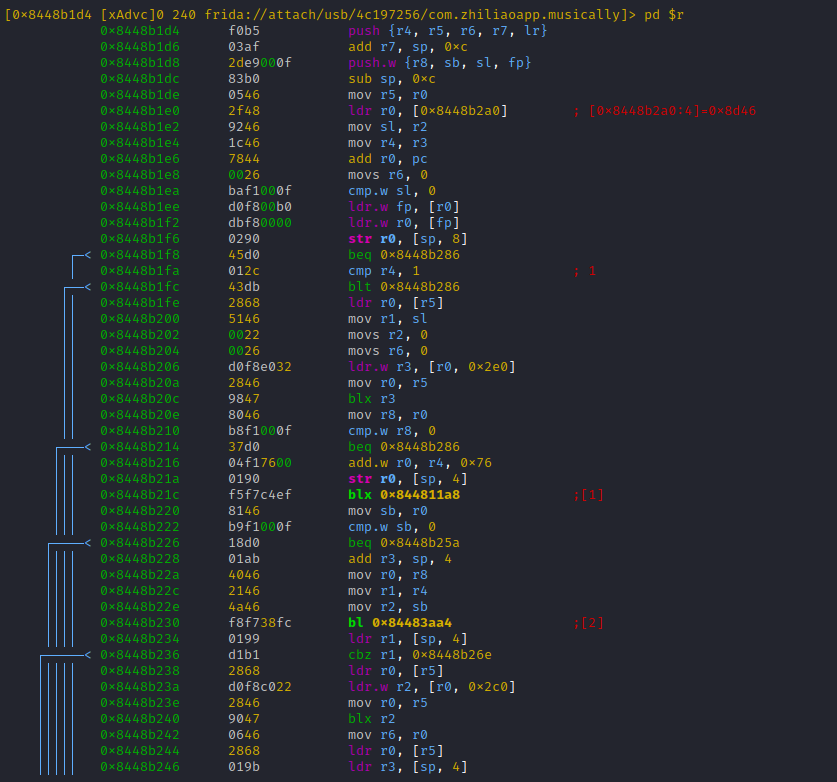
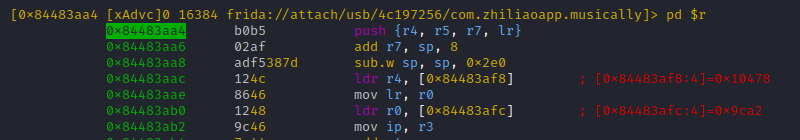
Arm 32 supports two instruction sets "ARM mode" (32bit) and "Thumb mode" (16bit) which could be used interchangebly
For ARM the LSB is 0 (even address)
For THUMB the LSB is 1 (odd address)
This means the function address 0x8448b1d5 homes code in THUMB mode (16bit), while the first instruction resides at 0x8448b1d4
(sorry if it gets a bit complicated, will be clear in a second)
No seriously, as explained, on arm32 we have to disassemble at [THUMB mode address - 1] = 0x8448b1d4
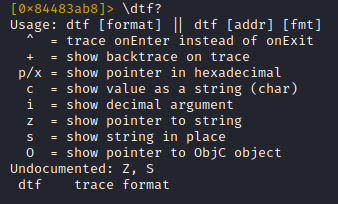
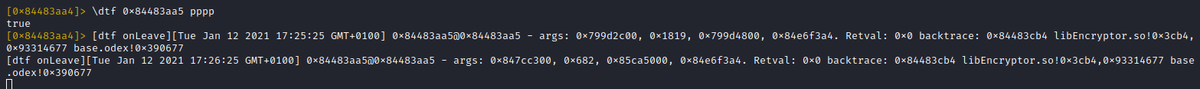
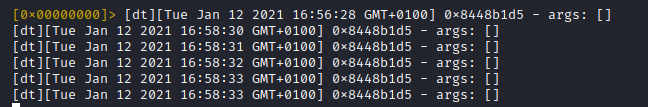
Now to get a feeling on how often this function is called, lets use 'r2frida' power to trace it.
Important: The thumb address has to be used here!!!
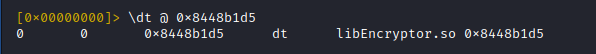
Some actions in the TikTok app ... trace logs for ttEncrypt-calls arrive
Trying to runtime-parse the function parameters, which represent Java object instances would be insane (maybe impossible)
It would be way easier to runtime-inspect these
Hitting [alt+1] moves us straight to the marked branch offset:
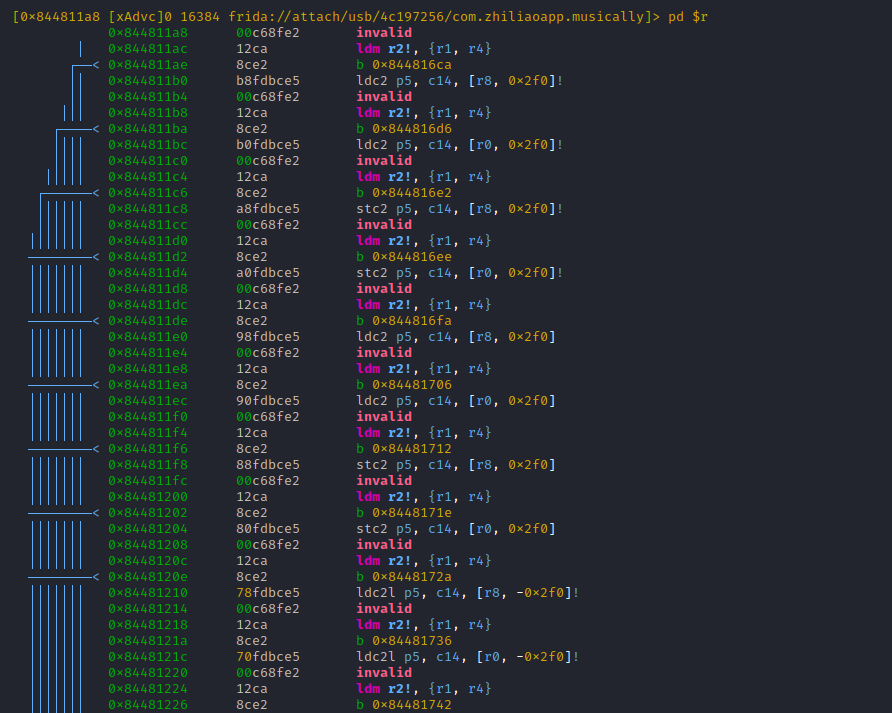
Hitting 'u' returns us to the parent function, followed by [alt+2] which brings us into the 2nd branch
More from Machine learning
10 PYTHON 🐍 libraries for machine learning.
Retweets are appreciated.
[ Thread ]

1. NumPy (Numerical Python)
- The most powerful feature of NumPy is the n-dimensional array.
- It contains basic linear algebra functions, Fourier transforms, and tools for integration with other low-level languages.
Ref: https://t.co/XY13ILXwSN
2. SciPy (Scientific Python)
- SciPy is built on NumPy.
- It is one of the most useful libraries for a variety of high-level science and engineering modules like discrete Fourier transform, Linear Algebra, Optimization, and Sparse matrices.
Ref: https://t.co/ALTFqM2VUo

3. Matplotlib
- Matplotlib is a comprehensive library for creating static, animated, and interactive visualizations in Python.
- You can also use Latex commands to add math to your plot.
- Matplotlib makes hard things possible.
Ref: https://t.co/zodOo2WzGx

4. Pandas
- Pandas is for structured data operations and manipulations.
- It is extensively used for data munging and preparation.
- Pandas were added relatively recently to Python and have been instrumental in boosting Python’s usage.
Ref: https://t.co/IFzikVHht4

Retweets are appreciated.
[ Thread ]

1. NumPy (Numerical Python)
- The most powerful feature of NumPy is the n-dimensional array.
- It contains basic linear algebra functions, Fourier transforms, and tools for integration with other low-level languages.
Ref: https://t.co/XY13ILXwSN
2. SciPy (Scientific Python)
- SciPy is built on NumPy.
- It is one of the most useful libraries for a variety of high-level science and engineering modules like discrete Fourier transform, Linear Algebra, Optimization, and Sparse matrices.
Ref: https://t.co/ALTFqM2VUo

3. Matplotlib
- Matplotlib is a comprehensive library for creating static, animated, and interactive visualizations in Python.
- You can also use Latex commands to add math to your plot.
- Matplotlib makes hard things possible.
Ref: https://t.co/zodOo2WzGx

4. Pandas
- Pandas is for structured data operations and manipulations.
- It is extensively used for data munging and preparation.
- Pandas were added relatively recently to Python and have been instrumental in boosting Python’s usage.
Ref: https://t.co/IFzikVHht4

Happy 2⃣0⃣2⃣1⃣ to all.🎇
For any Learning machines out there, here are a list of my fav online investing resources. Feel free to add yours.
Let's dive in.
⬇️⬇️⬇️
Investing Services
✔️ @themotleyfool - @TMFStockAdvisor & @TMFRuleBreakers services
✔️ @7investing
✔️ @investing_city
https://t.co/9aUK1Tclw4
✔️ @MorningstarInc Premium
✔️ @SeekingAlpha Marketplaces (Check your area of interest, Free trials, Quality, track record...)
General Finance/Investing
✔️ @morganhousel
https://t.co/f1joTRaG55
✔️ @dollarsanddata
https://t.co/Mj1owkzRc8
✔️ @awealthofcs
https://t.co/y81KHfh8cn
✔️ @iancassel
https://t.co/KEMTBHa8Qk
✔️ @InvestorAmnesia
https://t.co/zFL3H2dk6s
✔️
Tech focused
✔️ @stratechery
https://t.co/VsNwRStY9C
✔️ @bgurley
https://t.co/NKXGtaB6HQ
✔️ @CBinsights
https://t.co/H77hNp2X5R
✔️ @benedictevans
https://t.co/nyOlasCY1o
✔️
Tech Deep dives
✔️ @StackInvesting
https://t.co/WQ1yBYzT2m
✔️ @hhhypergrowth
https://t.co/kcLKITRLz1
✔️ @Beth_Kindig
https://t.co/CjhLRdP7Rh
✔️ @SeifelCapital
https://t.co/CXXG5PY0xX
✔️ @borrowed_ideas
For any Learning machines out there, here are a list of my fav online investing resources. Feel free to add yours.
Let's dive in.
⬇️⬇️⬇️
Investing Services
✔️ @themotleyfool - @TMFStockAdvisor & @TMFRuleBreakers services
✔️ @7investing
✔️ @investing_city
https://t.co/9aUK1Tclw4
✔️ @MorningstarInc Premium
✔️ @SeekingAlpha Marketplaces (Check your area of interest, Free trials, Quality, track record...)
General Finance/Investing
✔️ @morganhousel
https://t.co/f1joTRaG55
✔️ @dollarsanddata
https://t.co/Mj1owkzRc8
✔️ @awealthofcs
https://t.co/y81KHfh8cn
✔️ @iancassel
https://t.co/KEMTBHa8Qk
✔️ @InvestorAmnesia
https://t.co/zFL3H2dk6s
✔️
Tech focused
✔️ @stratechery
https://t.co/VsNwRStY9C
✔️ @bgurley
https://t.co/NKXGtaB6HQ
✔️ @CBinsights
https://t.co/H77hNp2X5R
✔️ @benedictevans
https://t.co/nyOlasCY1o
✔️
Tech Deep dives
✔️ @StackInvesting
https://t.co/WQ1yBYzT2m
✔️ @hhhypergrowth
https://t.co/kcLKITRLz1
✔️ @Beth_Kindig
https://t.co/CjhLRdP7Rh
✔️ @SeifelCapital
https://t.co/CXXG5PY0xX
✔️ @borrowed_ideas
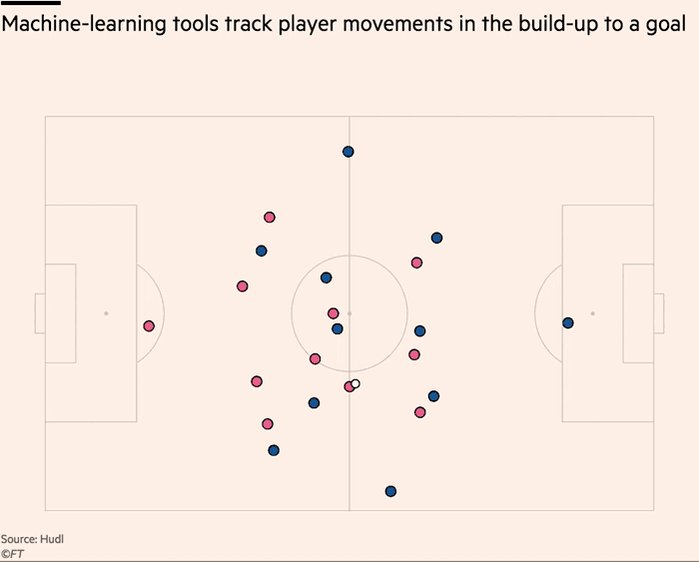
Really enjoyed digging into recent innovations in the football analytics industry.
>10 hours of interviews for this w/ a dozen or so of top firms in the game. Really grateful to everyone who gave up time & insights, even those that didnt make final cut 🙇♂️ https://t.co/9YOSrl8TdN
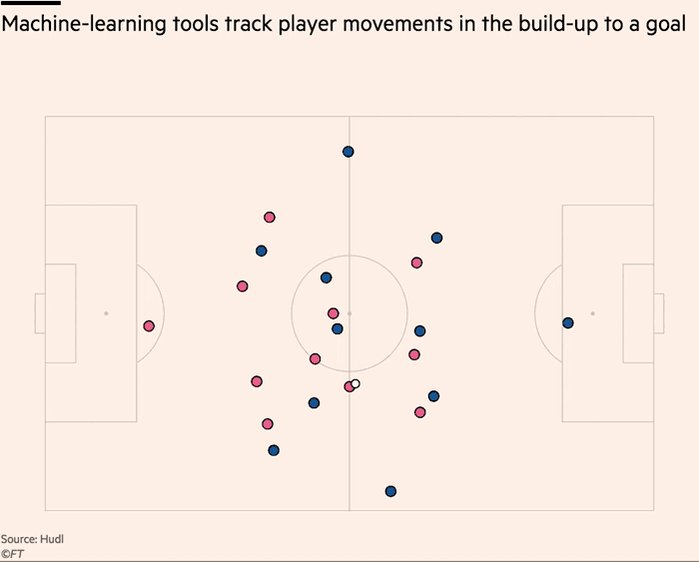
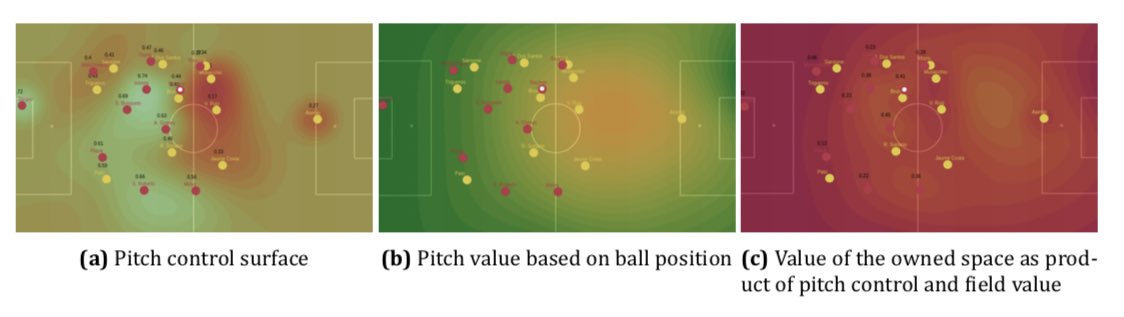
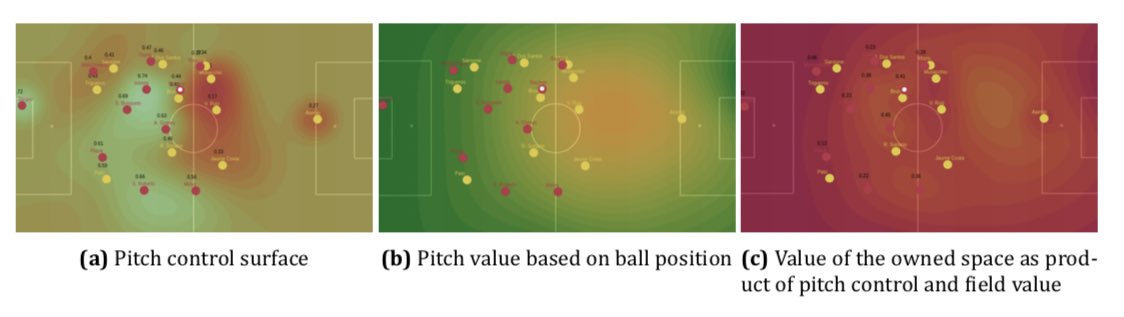
For avoidance of doubt, leading tracking analytics firms are now well beyond voronoi diagrams, using more granular measures to assess control and value of space.
This @JaviOnData & @LukeBornn paper from 2018 referenced in the piece demonstrates one method https://t.co/Hx8XTUMpJ5
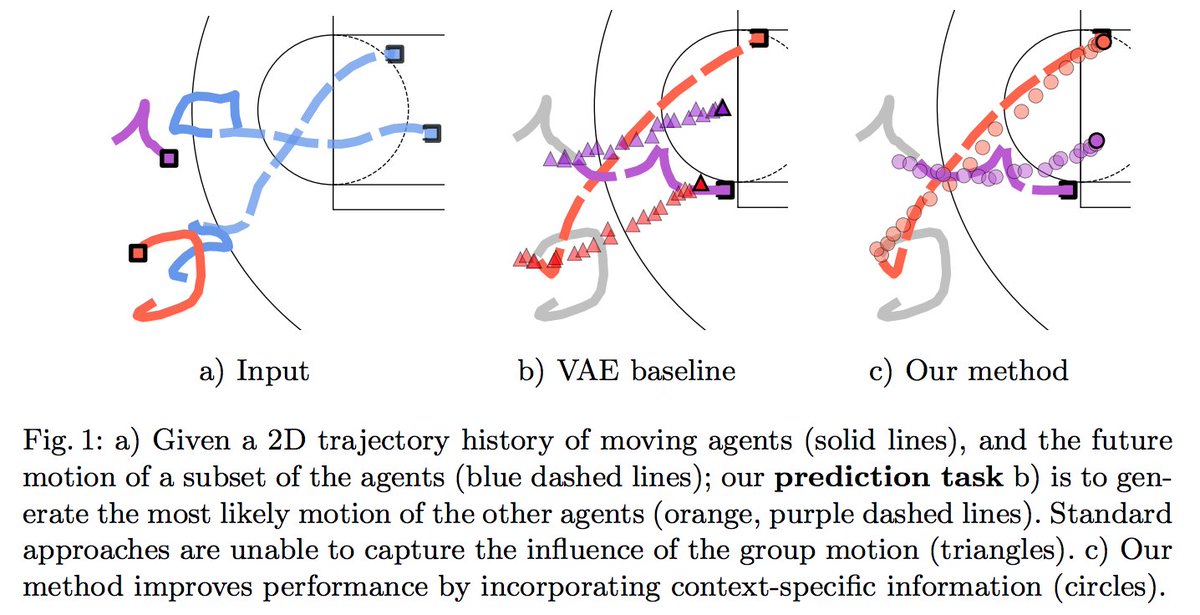
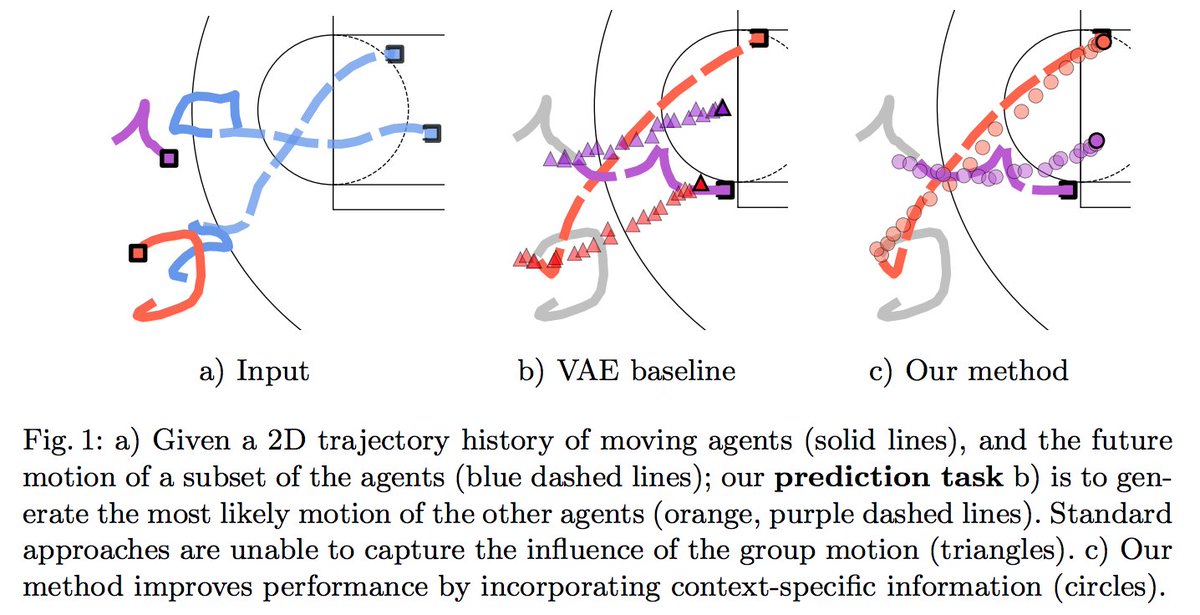
Bit of this that I nerded out on the most is "ghosting" — technique used by @counterattack9 & co @stats_insights, among others.
Deep learning models predict how specific players — operating w/in specific setups — will move & execute actions. A paper here: https://t.co/9qrKvJ70EN
So many use-cases:
1/ Quickly & automatically spot situations where opponent's defence is abnormally vulnerable. Drill those to death in training.
2/ Swap target player B in for current player A, and simulate. How does target player strengthen/weaken team? In specific situations?
>10 hours of interviews for this w/ a dozen or so of top firms in the game. Really grateful to everyone who gave up time & insights, even those that didnt make final cut 🙇♂️ https://t.co/9YOSrl8TdN
For avoidance of doubt, leading tracking analytics firms are now well beyond voronoi diagrams, using more granular measures to assess control and value of space.
This @JaviOnData & @LukeBornn paper from 2018 referenced in the piece demonstrates one method https://t.co/Hx8XTUMpJ5
Bit of this that I nerded out on the most is "ghosting" — technique used by @counterattack9 & co @stats_insights, among others.
Deep learning models predict how specific players — operating w/in specific setups — will move & execute actions. A paper here: https://t.co/9qrKvJ70EN
So many use-cases:
1/ Quickly & automatically spot situations where opponent's defence is abnormally vulnerable. Drill those to death in training.
2/ Swap target player B in for current player A, and simulate. How does target player strengthen/weaken team? In specific situations?